As I’ve mentioned in my other post for NDES implementation – The Ultimate Guide (check here), by design, Microsoft NDES role cannot be configured in HA-pair or a cluster out-of-the-box, you could instead put NDES nodes behind a load balancer, but since the challenge pasword is dynamically changing on each NDES node so the returning request from and end-point-device is not guaranteed to be routed by the load balancer to the same exact issuing NDES node, and the certificate sigining might fail in this case, so the other workround is to set a fixed challenge phrase accross all of your NDES nodes, and by then you will be able to have a highly-available, Active/Active NDES setup, but this is not secure at all (please read this TechNet post here). But, there’s a still a way around this by implementing a load balancer with a “Weighted routing” capability, so you can route all traffic to one node at a time, and it routes the traffic to the other (standby) node in case of a failure on the main node. Watch this video below for a demo about a running infrastructure with a highly-available NDES environment.
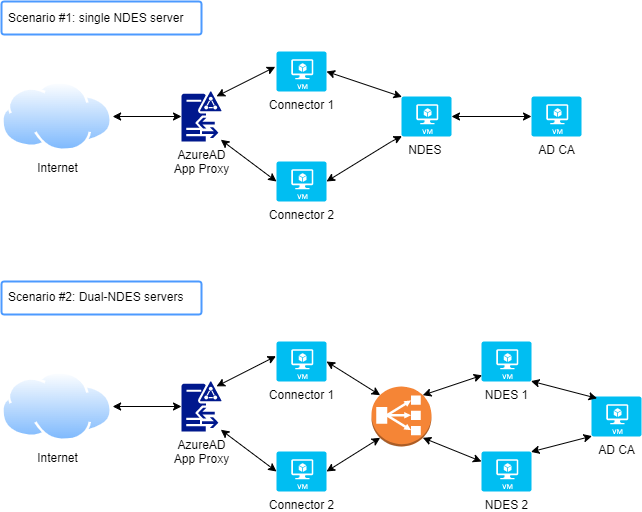
Node: if you are using Microsoft Intune as your MDM solution, then you don’t really to deploy this architecture as Intune has the capability of load-balancing the traffic accross multiple NDES servers (via Azure App Proxies)
Watxh the video for more details.